
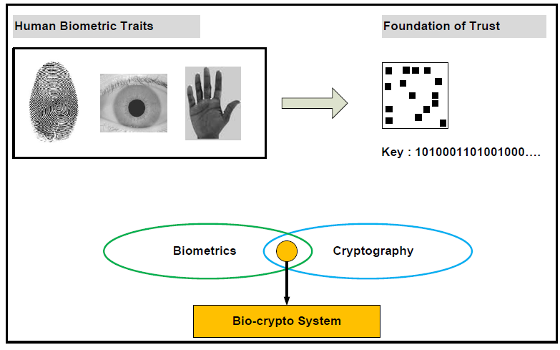
Cryptography Biometrics (Mainguet) intricated/entangled biometrics / La biométrie et la cryptographie : biométrie intriquée

Information Security-Based Nano- and Bio-Cryptography: Medicine & Healthcare Book Chapter | IGI Global

Generation of Cryptographic Keys from Personal Biometrics: An Illustration Based on Fingerprints | IntechOpen

Information Security-Based Nano- and Bio-Cryptography: Security & Forensics Book Chapter | IGI Global

Bio‐inspired and cognitive approaches in cryptography and security applications - Ogiela - 2018 - Concurrency and Computation: Practice and Experience - Wiley Online Library

Survey on Image Encryption Schemes, Bio cryptography and Efficient Encryption Algorithms | SpringerLink
An Enhanced Biometric Based Authentication with Key-Agreement Protocol for Multi-Server Architecture Based on Elliptic Curve Cryptography | PLOS ONE
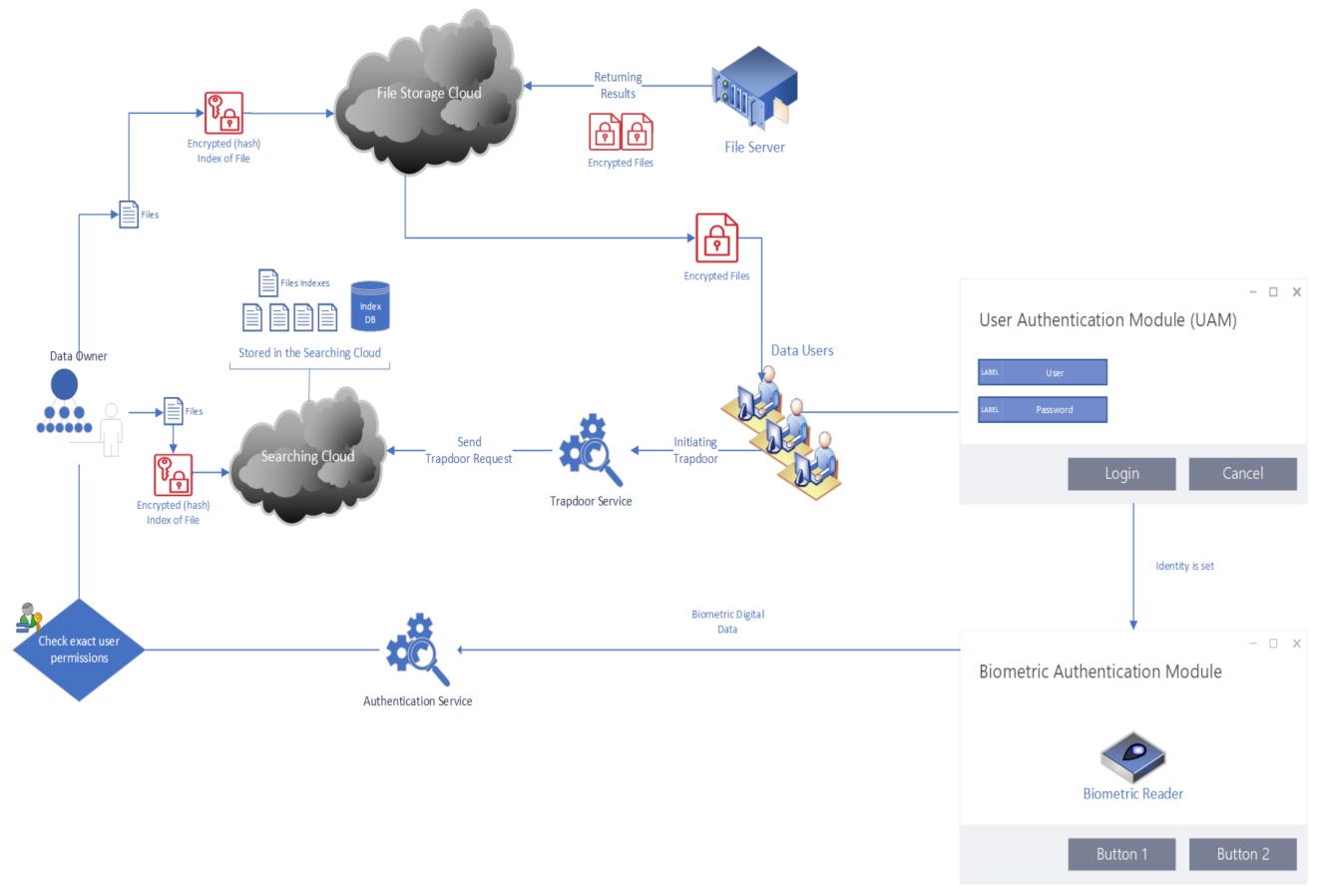
Cryptography | Free Full-Text | A Searchable Encryption Scheme with Biometric Authentication and Authorization for Cloud Environments | HTML
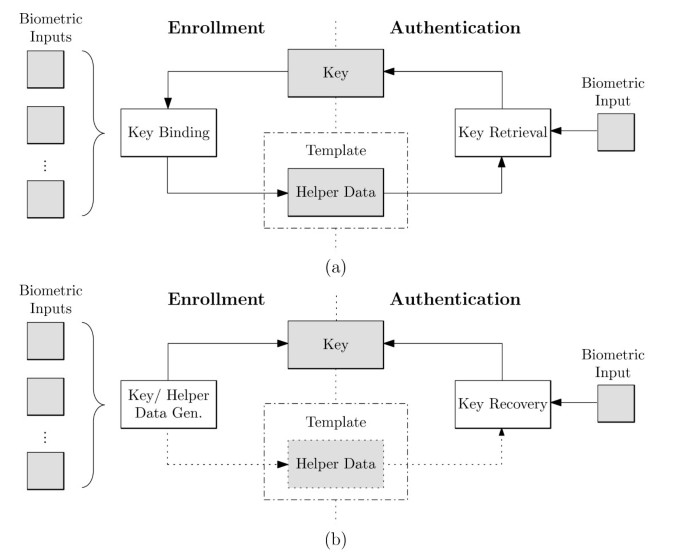
A survey on biometric cryptosystems and cancelable biometrics | EURASIP Journal on Information Security | Full Text
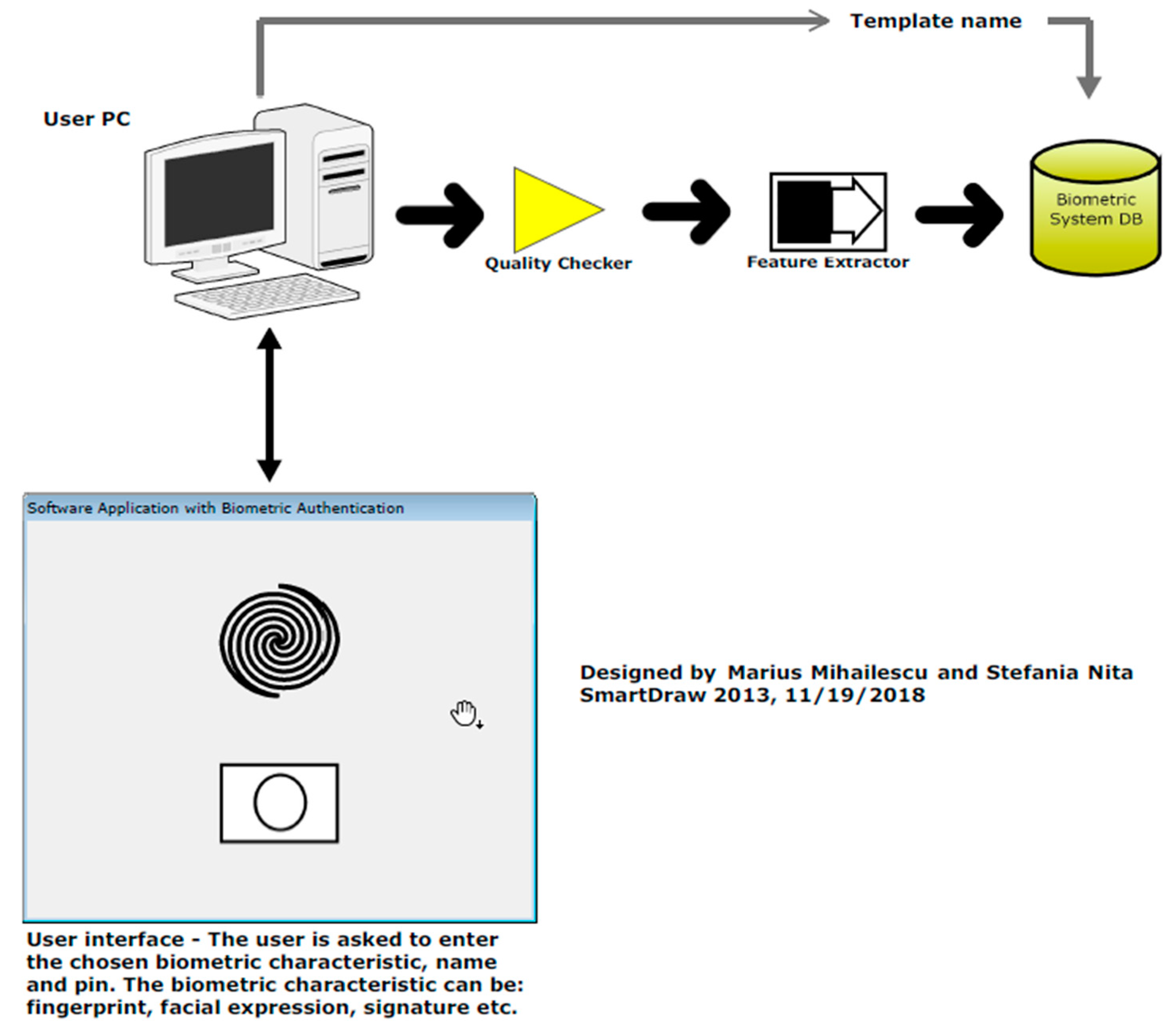









![PDF] Cloud Server Security using Bio-Cryptography | Semantic Scholar PDF] Cloud Server Security using Bio-Cryptography | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/bc61e01b8456b554de66f0ffd90dc66298f9e0fb/4-Figure4-1.png)
![PDF] Encryption Keys Generation Based on Bio-Cryptography Finger Vein Method | Semantic Scholar PDF] Encryption Keys Generation Based on Bio-Cryptography Finger Vein Method | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1b24b915d0d85b35d7fe0fc39b4d34eb917d8329/2-Figure1-1.png)
